“SIM swapping has become increasingly common over the past few years. This attack doesn’t require sophisticated scripting—it often requires just a little bit of background information on the victim to launch a devastating attack. ”
― Anonymous
SIM swapping attacks
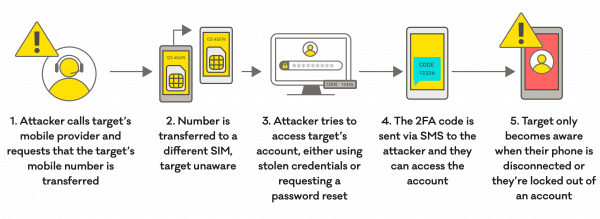
A SIM swap attack (also known as SIM porting or SIM hijacking) is where an attacker tricks a mobile phone service provider into transferring a customer’s phone number from the customer’s SIM card, to the attacker’s SIM card.
How can this happen?
This is done by an attacker pretending to be the customer, often using information gained from social media to answer security questions that the provider asks. Once the attacker has the target’s mobile phone number transferred to their SIM card, they can then access the target’s SMS messages or voice mails, all without the target knowing. There is a significant risk to those who are targeted because the attacker can use their access to the target’s number to perform sensitive tasks – like changing passwords and authorizing financial transactions.
An attacker may try to access the target’s accounts, like a bank account, either with stolen or guessed credentials. If the target is using SMS based two-factor authentication (2FA), the attacker can see the access code and can then access the account.
How will I know if I’m affected?
The first sign is likely to be a loss of connectivity on your cell phone. If your phone suddenly disconnects from your mobile providers network, you should investigate further. Have other people’s phones also disconnected, or just yours? If only you are affected, you should talk to your provider to see if they have made any changes to your account, especially setting up a new SIM card for your phone number. You may also notice suspicious activity on other accounts, like receiving un-prompted password reset notifications or getting locked out of your account/s.
How can I reduce the impact?
SIM swapping is tricky for people to prevent and detect but there are ways to reduce your chances of being a target.
- Be careful where you share identity information. Your personal information can be used to impersonate you, particularly when it’s used as part of the identity confirmation process. If you know that your mobile phone provider confirms your identity by asking for personal information, make sure it’s hard to find online. For example, you may be asked for your date of birth so make sure you’re not sharing it on your public social media accounts.
- Be creative with account recovery questions. For some services, when you set up your account you’ll be asked to provide answers to a set of security questions. These are generally used as a way to identify you if you forget your password and need a prompt — like your mother’s maiden name. Unfortunately, these are also easy things for an attacker to find out, and could be used to gain access to your accounts without your knowledge. Where you can, make up something memorable but untrue that an attacker couldn’t find through a simple search of your name. You can use a password manager to store these answers too.
- When there’s a choice, don’t use SMS two-factor authentication. SMS two-factor authentication is better than a password alone, but there are stronger options available. Ask your bank or service provider if they offer other forms of two-factor authentication for account access. For example, this might be an app-based authenticator that generates a new code every 60 seconds or sends you a push notification.
- Get notifications. Check with your bank about whether they have a system to notify you about suspicious account activity – like sending you an email any time there’s a request for a transaction over a certain value.
If you’re affected
If you’re affected, take the following steps immediately:
- Report it to your mobile phone provider and check if your mobile phone number has been transferred to another SIM.
- Reset passwords for your important online accounts. Online bank and email should be a priority.
- Report it to PNGCERT. We can help with advice to secure yourself. With your permission we can also work with the Police.
